A number of months in the past, I wrote in regards to the safety of AI fashions, fine-tuning methods, and the usage of Retrieval-Augmented Era (RAG) in a Cisco Security Blog post. On this weblog publish, I’ll proceed the dialogue on the essential significance of studying find out how to safe AI programs, with a particular deal with present LLM implementations and the “LLM stack.”
I additionally just lately revealed two books. The primary e-book is titled “The AI Revolution in Networking, Cybersecurity, and Emerging Technologies” the place my co-authors and I cowl the best way AI is already revolutionizing networking, cybersecurity, and rising applied sciences. The second e-book, “Beyond the Algorithm: AI, Security, Privacy, and Ethics,” co-authored with Dr. Petar Radanliev of Oxford University, presents an in-depth exploration of essential topics together with pink teaming AI fashions, monitoring AI deployments, AI provide chain safety, and the applying of privacy-enhancing methodologies corresponding to federated studying and homomorphic encryption. Moreover, it discusses methods for figuring out and mitigating bias inside AI programs.
For now, let’s discover among the key elements in securing AI implementations and the LLM Stack.
What’s the LLM Stack?
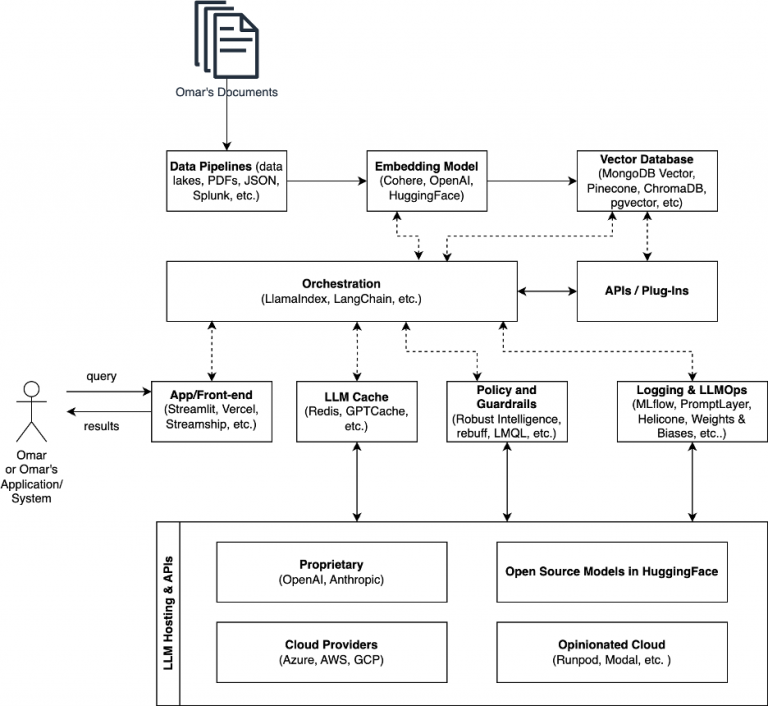
The “LLM stack” usually refers to a stack of applied sciences or parts centered round Giant Language Fashions (LLMs). This “stack” can embrace a variety of applied sciences and methodologies geared toward leveraging the capabilities of LLMs (e.g., vector databases, embedding fashions, APIs, plugins, orchestration libraries like LangChain, guardrail instruments, and so forth.).
Many organizations are attempting to implement Retrieval-Augmented Generation (RAG) these days. It is because RAG considerably enhances the accuracy of LLMs by combining the generative capabilities of those fashions with the retrieval of related data from a database or information base. I launched RAG in this article, however briefly, RAG works by first querying a database with a query or immediate to retrieve related data. This data is then fed into an LLM, which generates a response primarily based on each the enter immediate and the retrieved paperwork. The result’s a extra correct, knowledgeable, and contextually related output than what might be achieved by the LLM alone.
Let’s go over the everyday “LLM stack” parts that make RAG and different purposes work. The next determine illustrates the LLM stack.
Vectorizing Information and Safety
Vectorizing information and creating embeddings are essential steps in making ready your dataset for efficient use with RAG and underlying instruments. Vector embeddings, also referred to as vectorization, contain reworking phrases and several types of information into numerical values, the place each bit of information is depicted as a vector inside a high-dimensional area. OpenAI affords completely different embedding models that can be utilized by way of their API. It’s also possible to use open supply embedding models from Hugging Face. The next is an instance of how the textual content “Instance from Omar for this weblog” was transformed into “numbers” (embeddings) utilizing the text-embedding-3-small mannequin from OpenAI.
"object": "listing",
"information": [
{
"object": "embedding",
"index": 0,
"embedding": [
0.051343333,
0.004879803,
-0.06099363,
-0.0071908776,
0.020674748,
-0.00012919278,
0.014209986,
0.0034705158,
-0.005566879,
0.02899774,
0.03065297,
-0.034541197,
<output omitted for brevity>
]
}
],
"mannequin": "text-embedding-3-small",
"utilization": {
"prompt_tokens": 6,
"total_tokens": 6
}
}
Step one (even earlier than you begin creating embeddings) is information assortment and ingestion. Collect and ingest the uncooked information from completely different sources (e.g., databases, PDFs, JSON, log information and different data from Splunk, and so forth.) right into a centralized information storage system known as a vector database.
Word: Relying on the kind of information you will have to scrub and normalize the info to take away noise, corresponding to irrelevant data and duplicates.
Guaranteeing the safety of the embedding creation course of includes a multi-faceted method that spans from the choice of embedding fashions to the dealing with and storage of the generated embeddings. Let’s begin discussing some safety issues within the embedding creation course of.
Use well-known, business or open-source embedding fashions which were completely vetted by the neighborhood. Go for fashions which can be broadly used and have a powerful neighborhood help. Like all software program, embedding fashions and their dependencies can have vulnerabilities which can be found over time. Some embedding fashions might be manipulated by menace actors. This is the reason provide chain safety is so necessary.
You also needs to validate and sanitize enter information. The information used to create embeddings might comprise delicate or private data that must be protected to adjust to information safety laws (e.g., GDPR, CCPA). Apply information anonymization or pseudonymization methods the place attainable. Be certain that information processing is carried out in a safe surroundings, utilizing encryption for information at relaxation and in transit.
Unauthorized entry to embedding fashions and the info they course of can result in information publicity and different safety points. Use robust authentication and entry management mechanisms to limit entry to embedding fashions and information.
Indexing and Storage of Embeddings
As soon as the info is vectorized, the subsequent step is to retailer these vectors in a searchable database or a vector database corresponding to ChromaDB, pgvector, MongoDB Atlas, FAISS (Fb AI Similarity Search), or Pinecone. These programs permit for environment friendly retrieval of comparable vectors.
Do you know that some vector databases don’t help encryption? Guarantee that the answer you employ helps encryption.
Orchestration Libraries and Frameworks like LangChain
Within the diagram I used earlier, you possibly can see a reference to libraries like LangChain and LlamaIndex. LangChain is a framework for creating purposes powered by LLMs. It permits context-aware and reasoning purposes, offering libraries, templates, and a developer platform for constructing, testing, and deploying purposes. LangChain consists of a number of elements, together with libraries, templates, LangServe for deploying chains as a REST API, and LangSmith for debugging and monitoring chains. It additionally affords a LangChain Expression Language (LCEL) for composing chains and gives normal interfaces and integrations for modules like mannequin I/O, retrieval, and AI brokers. I wrote an article about quite a few LangChain assets and associated instruments which can be additionally accessible at one of my GitHub repositories.
Many organizations use LangChain helps many use instances, corresponding to private assistants, query answering, chatbots, querying tabular information, and extra. It additionally gives instance code for constructing purposes with an emphasis on extra utilized and end-to-end examples.
Langchain can work together with exterior APIs to fetch or ship information in real-time to and from different purposes. This functionality permits LLMs to entry up-to-date data, carry out actions like reserving appointments, or retrieve particular information from internet companies. The framework can dynamically assemble API requests primarily based on the context of a dialog or question, thereby extending the performance of LLMs past static information bases. When integrating with exterior APIs, it’s essential to make use of safe authentication strategies and encrypt information in transit utilizing protocols like HTTPS. API keys and tokens must be saved securely and by no means hard-coded into the applying code.
AI Entrance-end Functions
AI front-end purposes seek advice from the user-facing a part of AI programs the place interplay between the machine and people takes place. These purposes leverage AI applied sciences to supply clever, responsive, and customized experiences to customers. The entrance finish for chatbots, digital assistants, customized suggestion programs, and lots of different AI-driven purposes will be simply created with libraries like Streamlit, Vercel, Streamship, and others.
The implementation of conventional internet utility safety practices is crucial to guard in opposition to a variety of vulnerabilities, corresponding to broken access control, cryptographic failures, injection vulnerabilities like cross-site scripting (XSS), server-side request forgery (SSRF), and lots of different vulnerabilities.
LLM Caching
LLM caching is a method used to enhance the effectivity and efficiency of LLM interactions. You need to use implementations like SQLite Cache, Redis, and GPTCache. LangChain provides examples of how these caching strategies might be leveraged.
The fundamental thought behind LLM caching is to retailer beforehand computed outcomes of the mannequin’s outputs in order that if the identical or comparable inputs are encountered once more, the mannequin can shortly retrieve the saved output as an alternative of recomputing it from scratch. This could considerably cut back the computational overhead, making the mannequin extra responsive and cost-effective, particularly for often repeated queries or widespread patterns of interplay.
Caching methods have to be rigorously designed to make sure they don’t compromise the mannequin’s means to generate related and up to date responses, particularly in situations the place the enter context or the exterior world information adjustments over time. Furthermore, efficient cache invalidation methods are essential to stop outdated or irrelevant data from being served, which will be difficult given the dynamic nature of data and language.
LLM Monitoring and Coverage Enforcement Instruments
Monitoring is likely one of the most necessary parts of LLM stack safety. There are a lot of open supply and business LLM monitoring instruments corresponding to MLFlow. There are additionally a number of instruments that may assist shield in opposition to immediate injection assaults, corresponding to Rebuff. Many of those work in isolation. Cisco just lately introduced Motific.ai.
Motific enhances your means to implement each predefined and tailor-made controls over Personally Identifiable Info (PII), toxicity, hallucination, subjects, token limits, immediate injection, and information poisoning. It gives complete visibility into operational metrics, coverage flags, and audit trails, guaranteeing that you’ve a transparent oversight of your system’s efficiency and safety. Moreover, by analyzing consumer prompts, Motific lets you grasp consumer intents extra precisely, optimizing the utilization of basis fashions for improved outcomes.
Cisco additionally gives an LLM safety safety suite inside Panoptica. Panoptica is Cisco’s cloud utility safety resolution for code to cloud. It gives seamless scalability throughout clusters and multi-cloud environments.
AI Invoice of Supplies and Provide Chain Safety
The necessity for transparency, and traceability in AI improvement has by no means been extra essential. Provide chain safety is top-of-mind for a lot of people within the trade. This is the reason AI Invoice of Supplies (AI BOMs) are so necessary. However what precisely are AI BOMs, and why are they so necessary? How do Software program Payments of Supplies (SBOMs) differ from AI Payments of Supplies (AI BOMs)? SBOMs serve a vital function within the software program improvement trade by offering an in depth stock of all parts inside a software program utility. This documentation is crucial for understanding the software program’s composition, together with its libraries, packages, and any third-party code. Then again, AI BOMs cater particularly to synthetic intelligence implementations. They provide complete documentation of an AI system’s many parts, together with mannequin specs, mannequin structure, meant purposes, coaching datasets, and extra pertinent data. This distinction highlights the specialised nature of AI BOMs in addressing the distinctive complexities and necessities of AI programs, in comparison with the broader scope of SBOMs in software program documentation.
I published a paper with Oxford College, titled “Towards Reliable AI: An Evaluation of Synthetic Intelligence (AI) Invoice of Supplies (AI BOMs)”, that explains the idea of AI BOMs. Dr. Allan Friedman (CISA), Daniel Bardenstein, and I introduced in a webinar describing the function of AI BOMs. Since then, the Linux Basis SPDX and OWASP CycloneDX have began engaged on AI BOMs (in any other case generally known as AI profile SBOMs).
Securing the LLM stack is crucial not just for defending information and preserving consumer belief but in addition for guaranteeing the operational integrity, reliability, and moral use of those highly effective AI fashions. As LLMs turn into more and more built-in into numerous elements of society and trade, their safety turns into paramount to stop potential unfavorable impacts on people, organizations, and society at giant.
Join Cisco U. | Be a part of the Cisco Learning Network.
Comply with Cisco Studying & Certifications
Twitter | Facebook | LinkedIn | Instagram | YouTube
Use #CiscoU and #CiscoCert to affix the dialog.
Share:







